 Covering COVID-19 is a daily Poynter briefing of story ideas about the coronavirus and other timely topics for journalists, written by senior faculty Al Tompkins. Sign up here to have it delivered to your inbox every weekday morning.
Covering COVID-19 is a daily Poynter briefing of story ideas about the coronavirus and other timely topics for journalists, written by senior faculty Al Tompkins. Sign up here to have it delivered to your inbox every weekday morning.
The White House’s warnings about what Russia will do next have been ominously accurate so far, so this warning from President Joe Biden should put businesses, governments, utilities, hospitals and, yes, news organizations on alert:
I’ve previously warned about the potential that Russia could conduct malicious cyber activity against the U.S. Today, I’m reiterating those warnings based on evolving intelligence that the Russian Government is exploring options for potential cyberattacks. https://t.co/wO2jJgg5SJ
— President Biden (@POTUS) March 21, 2022
Biden said Monday:
Most of America’s critical infrastructure is owned and operated by the private sector and critical infrastructure owners and operators must accelerate efforts to lock their digital doors. The Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) has been actively working with organizations across critical infrastructure to rapidly share information and mitigation guidance to help protect their systems and networks
If you have not already done so, I urge our private sector partners to harden your cyber defenses immediately.
This is a quick guide to how to respond to a cyberattack. It would be interesting to ask how local governments, utilities and essential services in your community have practiced responding to a cyberattack — if they have.
The U.S. got a taste of what such an attack might do in 2021 when Russia-based cybercriminals hacked into the IT network of Colonial Pipeline. Colonial paid a $5 million ransom to get the system back online.
At the same time, NBC News says, the American government has also been working on plans to launch a cyberattack on Russia. NBC News reports:
Two U.S. intelligence officials, one Western intelligence official and another person briefed on the matter say no final decisions have been made, but they say U.S. intelligence and military cyber warriors are proposing the use of American cyberweapons on a scale never before contemplated. Among the options: disrupting internet connectivity across Russia, shutting off electric power, and tampering with railroad switches to hamper Russia’s ability to resupply its forces, three of the sources said.
“You could do everything from slow the trains down to have them fall off the tracks,” one person briefed on the matter said.
Russia was involved in cyberattacks on Ukraine’s power grid in 2015 and 2016. Vox notes:
In 2017, Kremlin-linked hackers launched a different kind of a cyberattack in Ukraine: a ransomware program known as NotPetya, which encrypted any data it reached, leaving the data’s unsuspecting owner locked out from accessing their own files. Victims were told to pay a ransom of $300 in bitcoin if they wanted access to their data returned. But the ransomware attack spread beyond Ukraine’s borders, infecting computer networks of companies around the world. According to a former US official, the attack resulted in more than $10 billion in total loss in damages, and the NotPetya attack is now regarded as one of the worst cyberattacks in modern history.
Last week, a cyberattack on an Israeli telecommunications provider forced a state of emergency after it knocked out government websites. The attack likely came from Iran, experts said. Cyber experts say they are preparing for an attack on U.S. satellites and are already investigating whether Russia was involved in a recent satellite attack.
Cyber experts interviewed by USA Today offer these guidelines for everyone, including newsrooms, to adopt:
Update everything, including software
Update antivirus and malware software, operating systems and applications, especially web browsers, on all devices including mobile phones, tablets, desktop computers and laptops. Turn on automatic updates.
Think before you click
Before clicking or tapping on links or attachments or downloading files, take a beat. Most cyberattacks start with a phishing email, which looks legitimate but isn’t and can be used to steal your passwords, Social Security number, credit card numbers and other sensitive information or to run malicious software known as malware.
Use strong, unique passwords
Use strong passwords and don’t reuse them. Your best bet is to subscribe to a password manager to generate and store unique passwords.
Back up important files now
Cybersecurity professionals urge Americans to back up important files such as bank accounts and statements in the cloud and on external drives.
Use a VPN on public internet
Use a VPN, or virtual private network. It provides an additional layer of protection between your devices and the internet by hiding your IP address and your location. It also encrypts your data.
Also, make sure your home Wi-Fi is password protected and secure to keep people from stealing your personal information and attacking your devices.
One of the single most important things you can update and secure is the router(s) that your home and office depend on. AVG.com explains:
To launch a large-scale cyberattack, attackers need a botnet: in other words, a loose network of connected devices. This could be your laptop, your mobile, your Smart TV … heck, even your smart toaster — infected to act as one in carrying out attacks against companies, power grids, or ultimately the world. And the reality is that the first line of defense all of these internet-enabled devices have is your router.
Yeah, that’s right: your router. That weird clunky box you have hiding under your couch or behind your desk breathing dust, forgotten by you, your internet service provider and in all likelihood its makers — that’s your unlikely hero, right there.
But it can also be your weakest link unless you take steps now to make sure it’s working for you, and not them. You’d be surprised how unsecure routers are out of the box. The good news is that hackers usually go for the low-hanging fruit. Just a few improvements to your router security can make you an unappealing target.
Open your router settings page and do this:
- Change the default admin username and password for your router.
- Turn on WPA2 encryption.
- Disable any remote access services.
- Make sure you trust all the devices that you connect to your network.
Even if this sounds a little like end-of-times survivalist stuff, the cyber experts say prepare for cyberattacks the same way you prepare (or should prepare) for natural emergencies. Sock away some cash, food and water. In an electrical grid attack, you might not be able to use a credit card or swipe a phone. My family keeps 30 days of military meals stored away for hurricanes. These things last 10 years and they just seem like a good idea. We also have five gallons of potable water stored for each person in the house. We keep two propane tanks full in case we need to grill out. We keep a generator serviced and ready to run and enough fuel to run it for three days.
Would a cyberattack cause a headache? Sure, but we would have food, water and electricity. It is not a terrible idea to keep your car’s gas tank more full than empty — you saw what could happen in an attack on the gasoline pipelines.
The point is, as the president says, to do what you can to be ready for whatever comes. If nothing comes, you will be ready for a wildfire, tornado, hurricane and whatever else in the seasons ahead.
US gun sales increase with Russian invasion of Ukraine
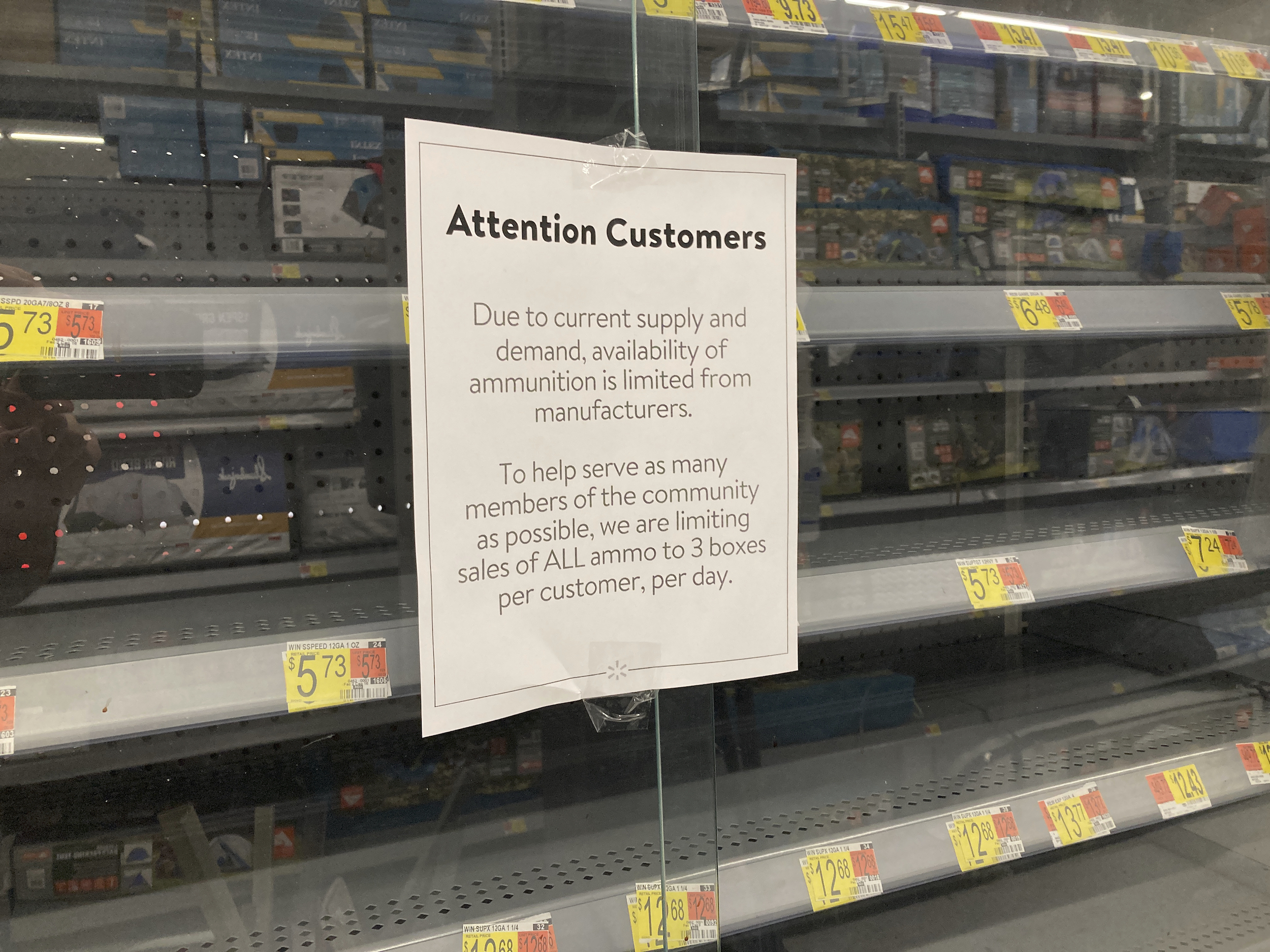
A sign in front of an empty bullet display case informs customers of purchase limits on gun ammunition at a Walmart store in Rochester, New York, on Monday, May 3, 2021. (AP Photo/Ted Shaffrey)
Gun buyers, on the whole, do not need much of a reason to buy more guns, but the latest data from Small Arms Analytics and Forecasting says Russia’s invasion of Ukraine sparked a jump in gun sales in the U.S. The increase is keyed to the very day Vladimir Putin launched the invasion:
SAAF Chief Economist Jurgen Brauer comments that “the estimated U.S. firearms unit sales for February 2022, although in line with the general seasonal pattern seen in the industry, were higher than might have been anticipated given the recent post-covid-19 pandemic sales slowdown. However, it is noticeable that the number of daily NICS background checks conducted on February 24th, 25th , 26th, and 28th (Thursday, Friday, Saturday, and Monday) were unusually high, coinciding with the beginning of Russia’s invasion of Ukraine.”
Preppers are back in style
Researching the cyberattack item got me poking around some “prepper” websites. It seems that the preppers are back at work stockpiling and preparing for the worst since Russia invaded Ukraine. Vice News reports:
The general manager of the Texas-based Rising S Company had to help install a 1,600-square-foot model, which goes for a touch over $300,000. He told VICE News during his lunch break at the local Taco Bell that his company received over 700 inquiries recently, in a time frame where they typically would have received about 10.
John Ramey, the founder of the prepper website The Prepared and a former Obama White House adviser, said the community has doubled in the last few years and pointed to a pre-pandemic FEMA study that showed the number of American citizens preparing for some sort of disaster increased from 3.8 percent in 2017 to 5.2 percent in 2019.
Traffic is also picking up on the r/preppers subreddit and Facebook pages “Prepping for Beginners” and “Doomsday Preppers Worldwide” have picked up steam.
Election workers are worried, intimidated and quitting
A new survey by The Brennan Center for Justice found, “1 in 5 local election officials are ‘very’ or ‘somewhat unlikely’ to continue serving through 2024.” The election workers cited “politicians’ attacks on the system” and “stress” as key reasons they will quit. The survey found “1 in 6 local election officials have experienced threats, and more than half of these cases have not been reported to law enforcement.” The study also found:
- More than 3 in 4 local election officials feel that threats against local election officials have increased in recent years.
- Nearly 1 in 3 know of at least one election worker who has left their job at least in part because of fears for their safety, increased threats, or intimidation.
- 3 in 5 are concerned that threats and harassment will make it harder to retain or recruit election workers going forward.
- More than half worry that incoming local election officials might buy into the “widespread fraud” narrative of the 2020 elections.
Despite the hassles and threats, most election workers say they are enthusiastic about their work during elections and see it as an important public service.
1,499 cases of threats, harassment of public health workers during the pandemic
The American Journal of Public Health is just out with a new report documenting threats, harassment and workplace violence against public health care workers during the pandemic. The study says of the hundreds of health care officials who quit in the last year, nearly one in four resignations was connected to an incident of harassment or threat. Stat summarizes the report:
The survey results were troubling: Health officials said they were personally attacked, villainized, and their experiences often marginalized. Their work was, at best, underappreciated, and, at worst, blamed for broader problems. Of those who said they’d experienced harassment, 24% reported facing backlash on social media; 6% said they had received personally targeted messages; 6% said they received threats to their own safety or their family’s; and 2% said their personal information was publicly shared online, a type of attack known as doxxing.
“I get threatening messages from people saying they are watching me. They followed my family to the park and took pictures of my kids,” one official quoted in the study said. “I know it’s my job to be out front talking about the importance of public health — educating people, keeping them safe. Now it kind of scares me… when they start photographing my family in public, I have to think is it worth it?”
‘Eating out’ confidence is high, but sales have not returned

Patrons Fe Copper with Lucky, left, and friend Ria Patterson with Gianni drink coffee at the Grand Central Los Angeles in Los Angeles Friday, March 4, 2022. (AP Photo/Damian Dovarganes)
New surveys found the overwhelming majority of Americans say they feel safe eating out at restaurants, which makes restaurant owners wonder why sales have not rebounded to pre-pandemic levels. There may be a few factors, including the cost of gasoline, that make “going out” more expensive. Households also don’t have the pandemic-era stimulus money they had a year ago, and menu prices may be a factor.
We’ll be back tomorrow with a new edition of Covering COVID-19. Are you subscribed? Sign up here to get it delivered right to your inbox.